Perhaps the following entry will tell you if it’s possible to you to become an ethical hacker, how to start your adventure and why you should be interested in it.
We all know what hackers do. Everyone who knows what hackers do, probably want to be a hacker too. The best hackers have great knowledge about the construction of networks, computer systems and applications. In addition, they know a few programming languages very well and rest understand on the basic level. Inquisitiveness, accuracy and awareness as well as vast knowledge in the wide field of computer science allows hackers to find bugs and exploit vulnerabilities. Searching for software bugs, configuration errors, badly secured servers. Testing the operation of programs, scanning networks, analyzing the source code of programs. All that to break into computer systems. Obtain unauthorized access to get sensitive data (or for fame and money).

A security hacker is someone who explores methods for breaching defenses and exploiting weaknesses in a computer system or network. Hackers may be motivated by a multitude of reasons, such as profit, protest, information gathering, challenge, recreation or to evaluate system weaknesses to assist in formulating defenses against potential hackers. The subculture that has evolved around hackers is often referred to as the computer underground.
If you want know more about security hacking and classification of hackers check this nice Wikipedia article.
An ethical hacker (white hat hacker) is the security professional. Ethical hackers know how to find and exploit vulnerabilities, and weaknesses in various systems. Uses those skills consistent with the law to try to find vulnerabilities and fix them before the malicious hacker (black hat hacker) try to break in. Ethical hacker is someone like a penetration tester but with a greater range of activities and responsibilities. Difference between ethical hackers and real hackers is the legality.
Who can become an ethical hacker? Everyone with a passion for IT plus good network and programming knowledge. Acquire new knowledge and stay up to date with new technologies. You must develop all the time.
Why is it worth trying your hand on hacking? Because if you are good at it, you can find a well-paid job as an IT security specialist. If you are already working in the IT industry, you can use these skills not only at work, but also as a hobby and an additional source of income. Many companies offer rewards in bug bounty programs. As part of such a program, you can, according to the guidelines of a given company, test its security and for each detected vulnerability, bug or threat, receive a monetary reward or eg. a job.
If you already know what you should learn and why you want to do it, then you should start hacking and hack so that you do not have problems with the law.
Start learning from free or paid on-line courses. There is a lot of courses about Ethical Hacking on Udemy e-learning platform. Certificates from such courses are not worth much, but you will definitely learn what you need. Look on the web how to set up your own virtual lab for testing and learning. On most on-line courses it is shown how to set up a virtual network and virtual computers to improve your skills. In most cases, you only need a virtual machine with the Kali Linux system that contains a set of all the necessary tools (check other operating systems for hackers). Once you have mastered the tools, tests your skills on specially prepared applications like DVWA (Damn Vulnerable Web App) and WebGoat (a deliberately insecure web application maintained by OWASP) both designed to learn about web application security.
Once you feel confident try your hand at on-line platforms that offer tasks with different levels of difficulty.
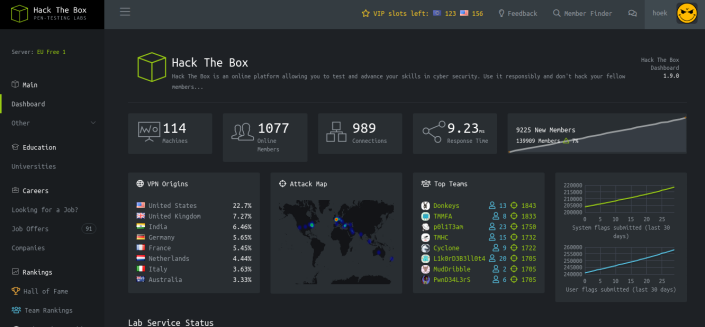
Hack The Box offers a lot of pen-testing labs ready to go. There are free and paid tasks from many different IT security areas. It is also nice community where you can exchange ideas and methodologies with thousands of people in the security field.
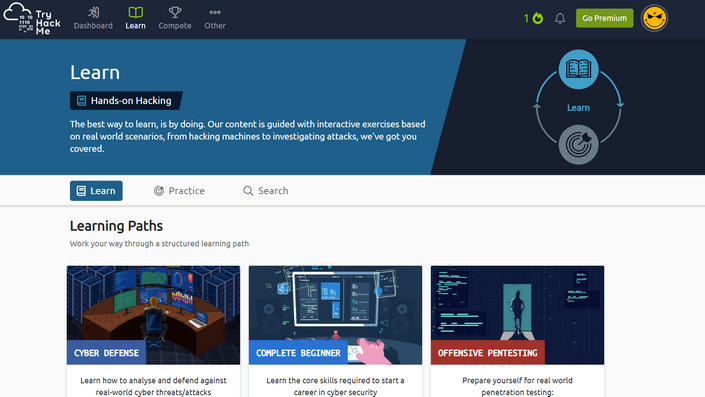
TryHackMe is awesome platform with free and paid security trainings and learning paths.
The next step are places where you can convert your skills into money.
Here are the pages on which you will find lists of bug bounty programs.
Vulnerability Lab - https://www.vulnerability-lab.com/list-of-bug-bounty-programs.php
Bug Crowd - https://www.bugcrowd.com/bug-bounty-list/
However, I recommend to start at HackerOne. Bug bounty platform for many well-known companies in one place. By browsing through reports and talking to other users, you can learn a lot.
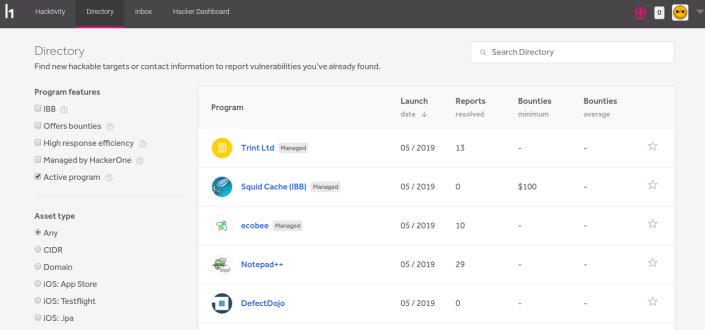
Whether you’re just getting started or have been hacking for decades, join the HackerOne Community to work directly with over 900 security teams and learn from peers who have accumulated over 50,000 resolved vulnerabilities in total. You can hack on web, APIs, Internet of Things (IoT), Android/iOS and anything else worth protecting.
Also you will get free copy of Peter Yaworski’s excellent Web Hacking 101 e-book when you sign up to for ethical hacking on HackerOne. It’s a great reading that will show you how to get started, how others started, where to grow and how to properly report your findings and create useful reports. On HackerOne you can also join course - Hacker101 - a free class on web security where anyone can learn how to hack.
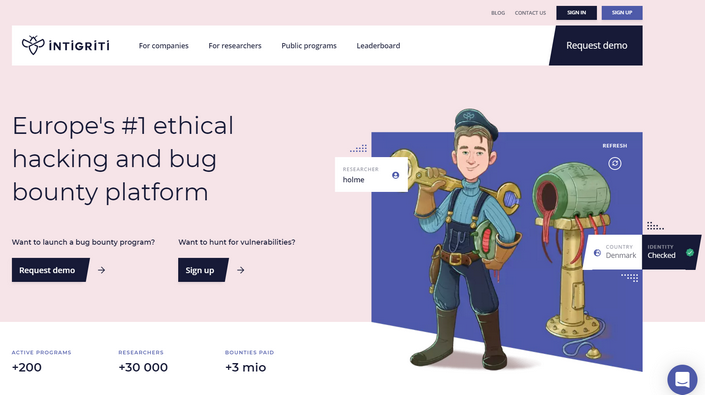
Similar place is Intigriti. You can find there some tutorials.
Learn to hack
Want to gain respect within the ethical hacking community? You’ll have to learn from the best. We’ll show you hacking techniques that you can’t learn elsewhere. You’ll learn how to outsmart and outmanoeuvre cybercriminals by thinking like one.
Read public reports to understand how someone found something.
Don’t be frightened by the amount of knowledge it takes to hack. Start with one topic and move on to the next. There is no one simple answer for how to get started. Just read, learn and click. Choose the topic that interests you the most, such as subdomain takeover, XSS or path traversal attacks or any other from OWASP Top Ten. Each of these topics is a really big dose of knowledge. Learn systematically. Use theories in practice. Do not give up. You looked for the vulnerability in one place, did it for several hours and found nothing, ok. Look elsewhere. Perhaps you do not have yet the right knowledge or what you are looking for does not exist. If you find something, keep track of the topic until you have no more ideas. Take notes, you might come back to the topic.
Check some interesting YouTube channels that can help you:
And that’s probably all for today. Get knowledge, read, learn and fulfill your dreams. If you have any tips and ideas, let me know.
Here is my Hack The Box website badge:
an TryHackMe:
Show me yours in comments!
Happy hacking or rather fruitful ;)

