I hope you haven’t forgotten about the Worth Checking series. Here you can check out the latest one. I thought I’d post monthly in this format, but it would turn out that I’d have more entries like this than my own :) If there were maybe 10 articles a month, it would make as much sense as possible. Maybe one day.
Welcome in episode 2.
As always, today’s header image was generated by AI. More documents and illustrations this time. All documents I found interesting or have on my reading list, enjoy!
Documents to check
- Threat Hunting Playbooks from MITRE Tactics
- A Guide of OS Command Injection
- RedTeam Scenarios
- A Detailed Guide on Kerbrute
- Activate Directory Security Guide
- Burp Suite For Pentester - HackBar
- Certified Professional Ethical Hacker Exam Guide
- CISO Handbook
- Cloud Security Guidance
- Comprehensive Guide on Honeypots
- Critical Exploits For Sale On The Dark Web
- Comprehensive Guide on TSHARK
- DNS Incident Response
- Email header analysis
- Forensic Investigation of Nmap Scan using Wireshark
- Incident Response Cheat Sheet
- Incident Response Playbooks And Workflows
- IoT Cybersecurity framework
- IoT Security Guide
- NSA and CISA Red and Blue Teams Share Top Ten Cybersecurity Misconfigurations
- Linux For Networking Professional
- Malware Analysis 101
- Network Security Best Practices
- NIST Storage Security Guide
- Nmap for Pentester - Output Format Scan
- Owasp Top Ten Vulnerabilities
- Penetration Testing Report
- Pentest Best Practice Checklist
- Pentesting Cheat Sheet
- Cisco - Secure Endpoints User Guide
- Shifting the Balance of Cybersecurity Risk
- SSH penetration Testing
- The Purple Book on Cyber Security
- The Coming AI Hackers
- Threats And Risk Management In The Health Sector
- Web Application Pentesting Checklist
- Windows Privilege Escalation - Server Operator Group
Articles to read
- Malrdp: Implementing rouge rdp manually
- BreachForums database and private chats for sale in hacker data breach
- Lessons from a newsroom raid: How to encrypt your devices to protect yourself
Bookmark this
Illustrations
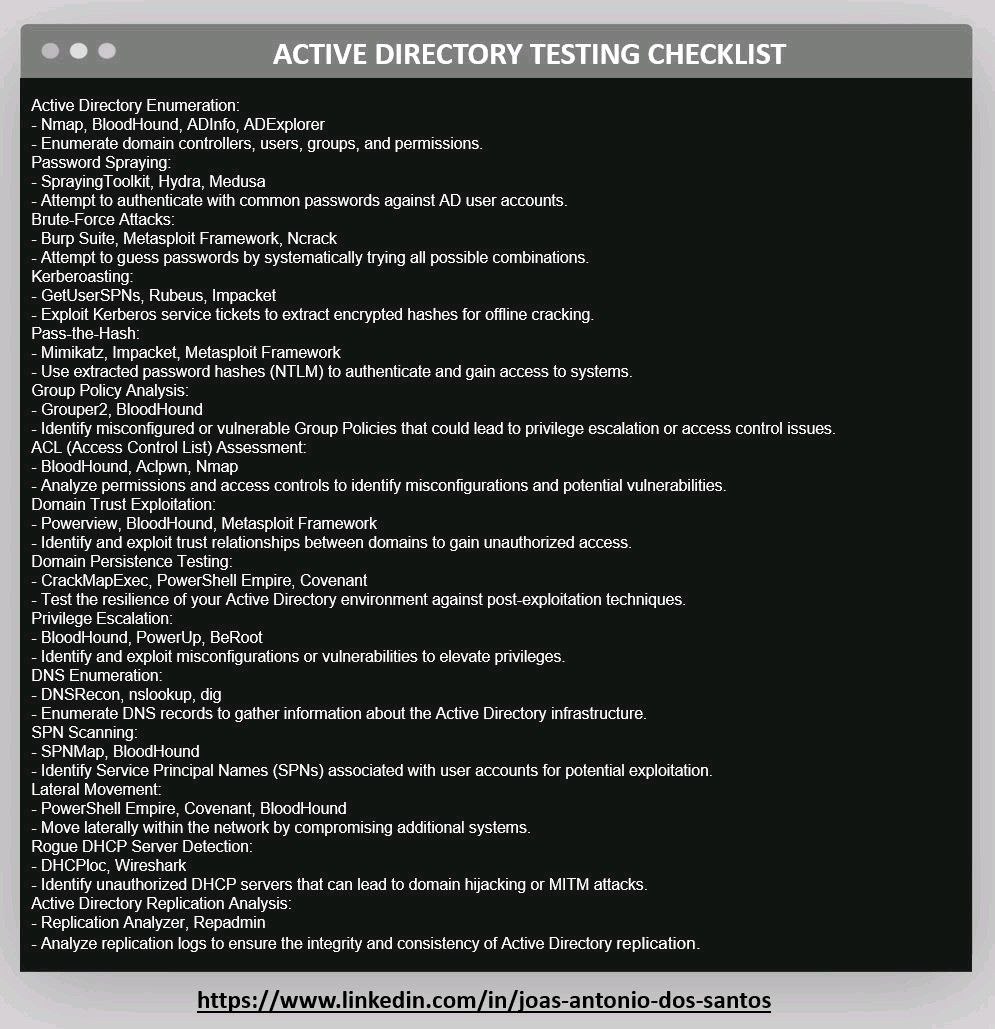
AD Testing Checklist
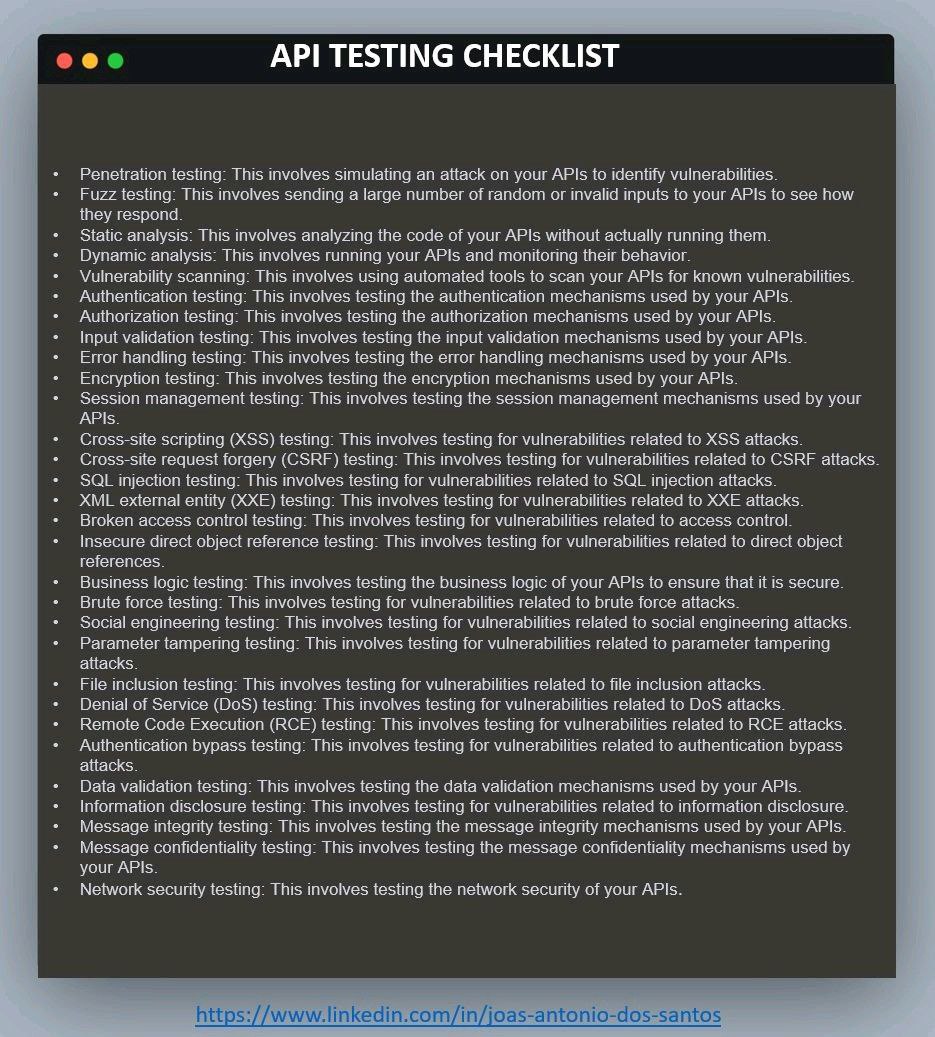
API Testing Checklist
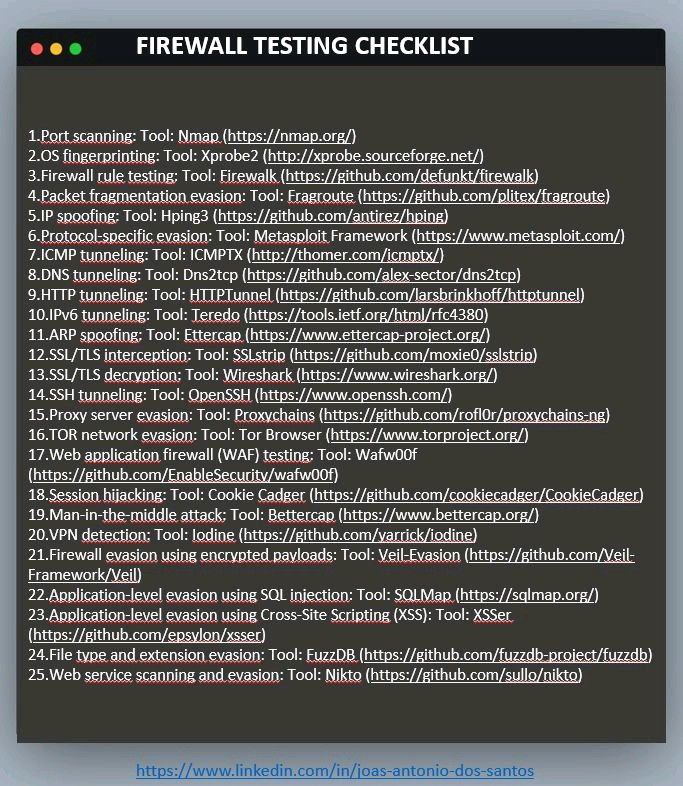
Firewall Testing Checklist
HTTP status codes
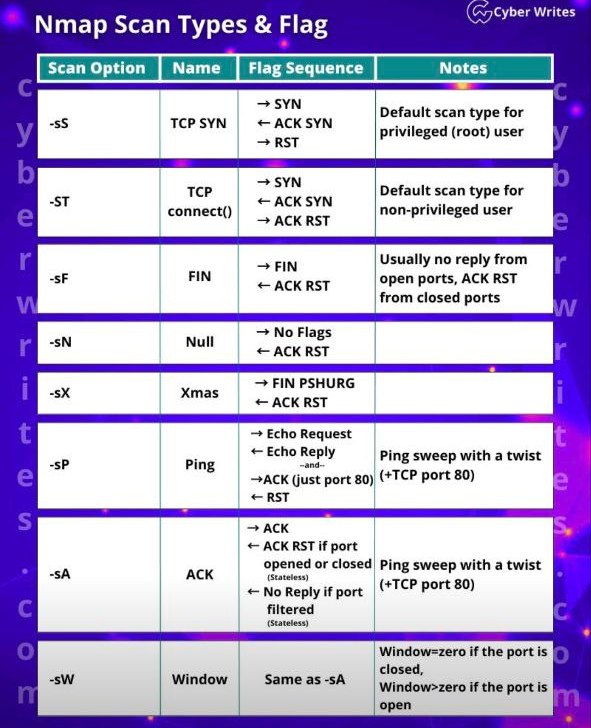
Nmap flags
Red Team Toolkit

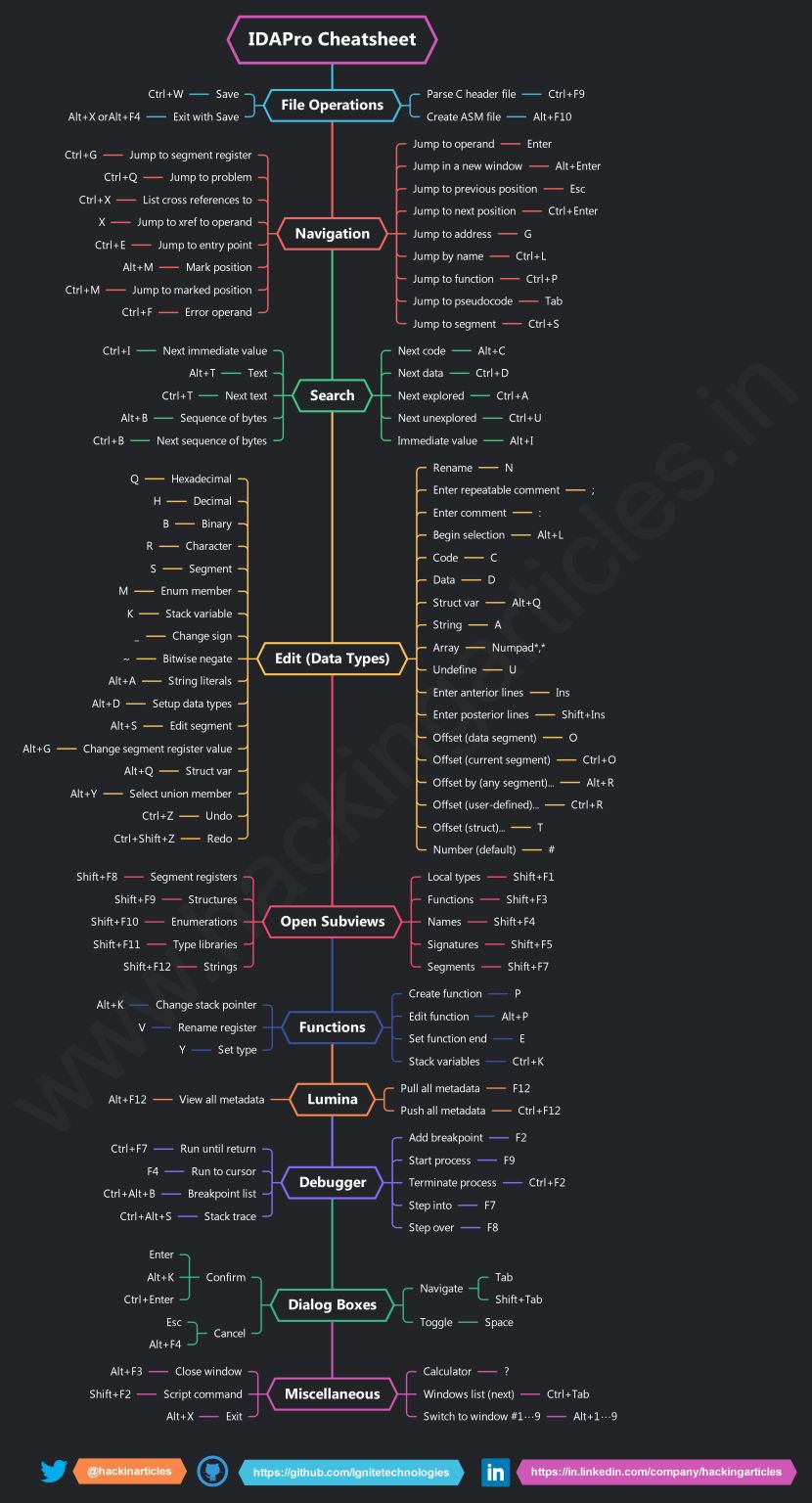
IDAPro Cheatsheet
Recon Tools for Web App Pentesting

20 API Security Tips

30 Cybersecurity Search Engines

Hacker search engines
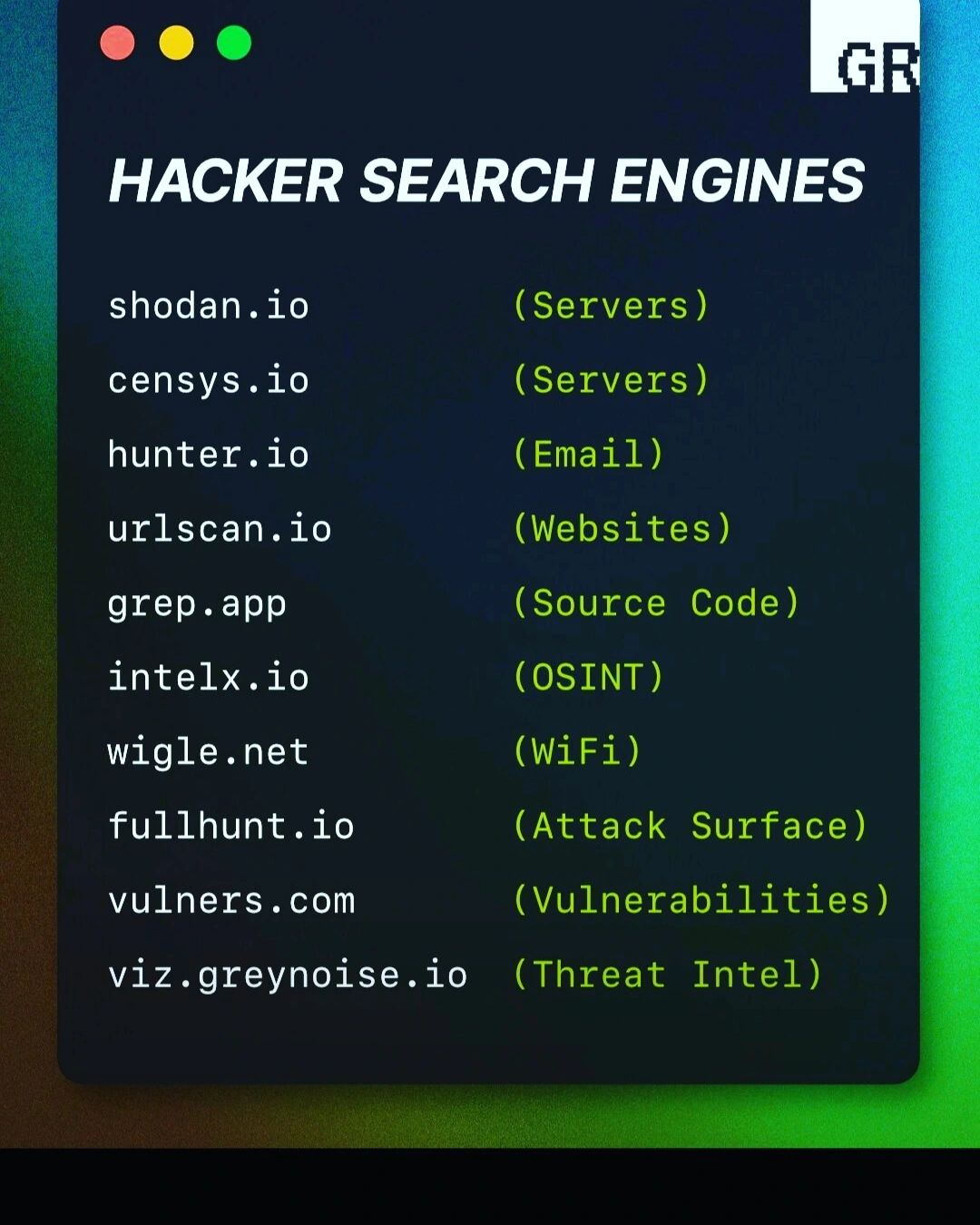
Search engines for cyber

Talking heads
Funny stuff
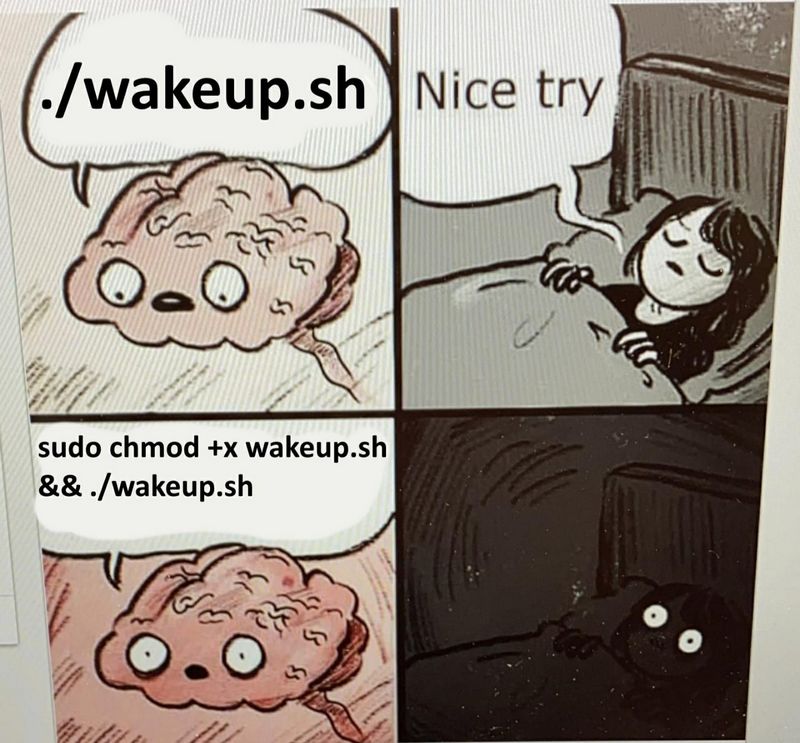
Brain comic
Interview

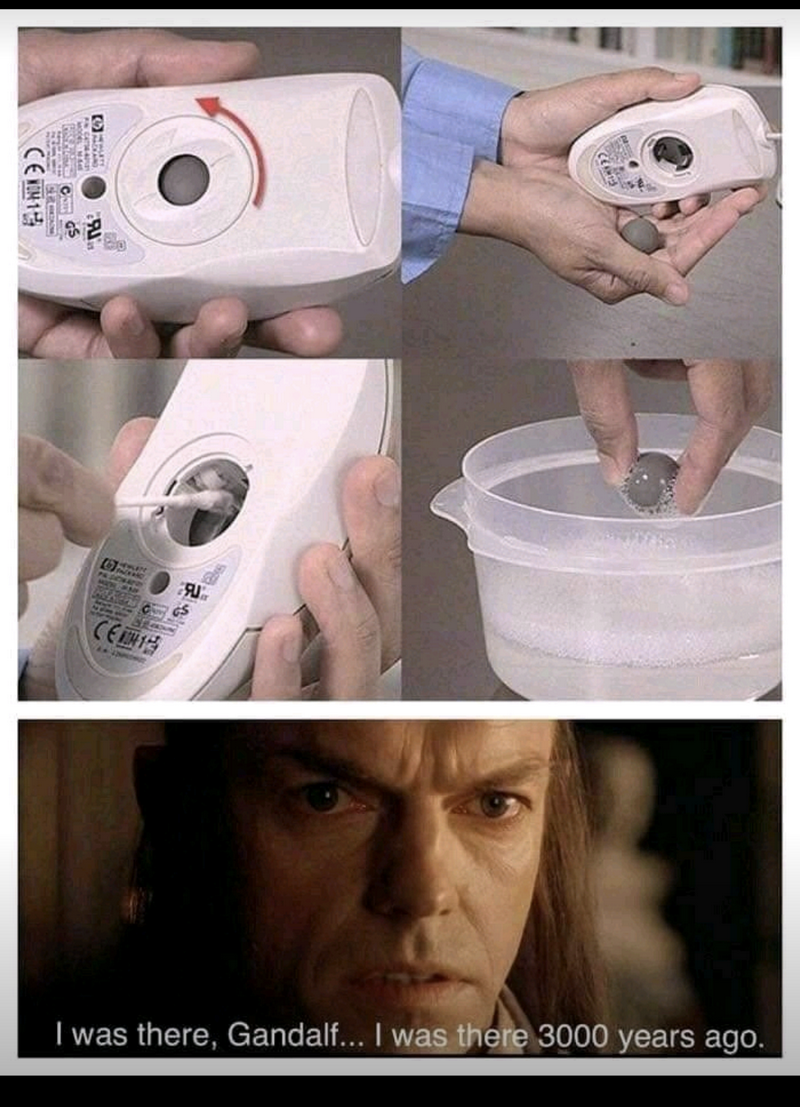
Mouse
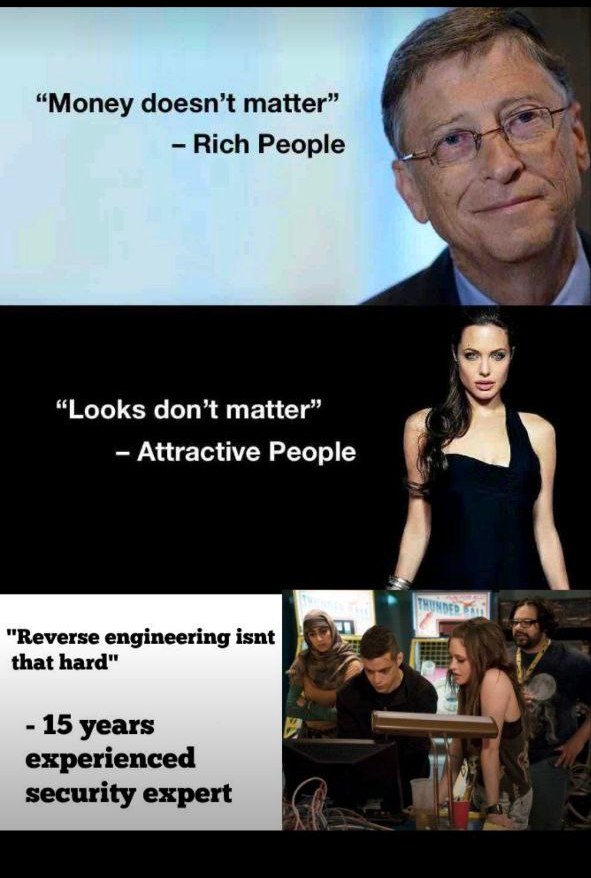
Reverse Engineering
T-Rex standup
